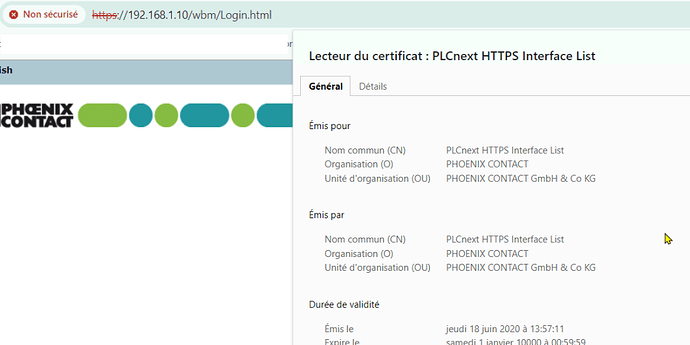
Here is another approach which will create new certificates which browsers approve:
First, you need to generate new certificates.
This can be done using the openssl command in the windows subsystem for Linux (WSL).
1: Create a new file with the below content. I use the nano command for this in the windows Power Shell for WSL:
nano san.cnf
Then populate the file with this content:
[req]
distinguished_name = req_distinguished_name
x509_extensions = v3_req
prompt = no
[req_distinguished_name]
CN = 192.168.1.10
O = ORGANIZATION
OU = UNIT
[v3_req]
You can list multiple IPs and DNS names, separated by commas
subjectAltName = IP:192.168.1.10, IP:192.168.2.10, IP:192.168.3.10, DNS:plc1.local, DNS:plc2.local, DNS:plc3.local
basicConstraints = CA:TRUE
keyUsage = keyEncipherment, digitalSignature, keyCertSign
extendedKeyUsage = serverAuth
subjectKeyIdentifier = hash
authorityKeyIdentifier = keyid,issuer
(Note, I have added the plc1.local to my windows hosts file to have an easier way to access the PLC - the dns entries might be removed if you’re not using them).
2: So, after creating this san.cnf file, run the following command to create certificate files (they will get plc.xxx names):
openssl req -x509 -nodes -days 1825 -newkey rsa:2048 -keyout plc.key -out plc.crt -config san.cnf -extensions v3_req
3: go to the WBM and find the certificate manager: In WBM2, this is in the left menu under Security → Certificate management. Open that page and select the tab named “identity stores”. In this list there is an item called HTTPS Self Signed. Expand it and press edit button. There are two rows, press edit on the top row and select your new plc.pem file. Press OK, and now the bottom line will complain as the key does not match. Edit the bottom line and upload the plc.crt file. All should be good now. Reboot the device.
4: Open the plc.crt file in windows and install the certificate in the trusted certificate store.
5: voila. You’ll get a nice padlock and no more nagging about insecure web page.